Patch Management Best Practices establish the foundation for reducing enterprise-wide risk, minimizing downtime, and maintaining regulatory compliance across endpoints, servers, and cloud resources, while aligning security operations with business priorities, IT service continuity, user productivity, asset lifecycle management, and governance so teams can respond proactively to evolving threat intelligence and supply chain risks. A well-structured program translates risk into actionable timelines, coordinates cross-functional teams across security, operations, and risk management, and ensures that patching activities fit within service level agreements, change control processes, and budget constraints while emphasizing predictable outcomes and auditable traceability. This approach emphasizes automation, repeatable workflows, and a risk-based prioritization strategy so critical assets receive timely updates without disruptive maintenance windows, backed by automation frameworks, configuration baselines, continuous monitoring, and a culture of proactive validation that reduces incident response time and strengthens overall resilience. In practice, you gain visibility through an accurate asset registry spanning on-premises and cloud environments, test patches in representative staging environments, verify installation success, monitor post-deployment performance, and document outcomes to support remediation efforts while maintaining user experience, service availability, and regulatory compliance. By weaving governance, dashboards, and continuous improvement into daily operations, organizations can accelerate patch cycles, demonstrate control to auditors, and sustain a resilient security posture that reduces exposure, supports regulatory requirements, and keeps business services reliable even as technology stacks evolve and new threats emerge.
From a liability reduction and resilience standpoint, this shifted framing emphasizes secure software updates, orderly patch rollouts, and governance-aligned change control to protect systems without sacrificing uptime. Using latent semantic indexing principles, we talk in terms of vulnerability management, software refresh cycles, remediation through timely updates, risk-based prioritization, and threat-informed strategies to keep networks resilient. Ultimately, the lifecycle mindset brings discovery, testing in staging environments, deployment validation, and continuous improvement into everyday operations to maintain compliance and minimize exposure.
Understanding Patch Management: Core Concepts and Business Value
Patch management is the disciplined process of identifying, acquiring, testing, and applying software updates to systems across the organization. It sits at the intersection of security and operations, and it directly ties to IT patch management and patch deployment best practices. When done right, it reduces exposure to known vulnerabilities, minimizes downtime, and supports compliant, auditable IT environments. This approach also aligns with software update management by treating patching as a repeatable business process rather than a one-off fix.
Organizations should view patch management through a risk-based lens, prioritizing patches based on exposure and impact. By mapping assets to CVEs, exploit likelihood, and asset criticality, teams can ensure that vulnerability remediation through patching is targeted where it matters most. Integrating patch management into standard IT workflows makes governance easier and helps demonstrate progress to stakeholders.
The Patch Management Lifecycle: From Inventory to Continuous Improvement
A successful program follows a lifecycle that starts with inventory and visibility. You cannot patch what you cannot see; therefore, maintaining an accurate asset registry across on-premises and cloud environments is essential. Discovery tools and endpoint agents support this foundation and reduce scanning noise, enabling focused remediation and a clearer view for IT patch management.
Next comes vulnerability assessment and risk scoring, patch discovery and prioritization, testing and staging, deployment and verification, and finally post-deployment governance. Each stage contributes to better change control, faster time to patch, and improved reliability, all of which are central to a mature patch management guide.
Patch Management Best Practices for IT Resilience
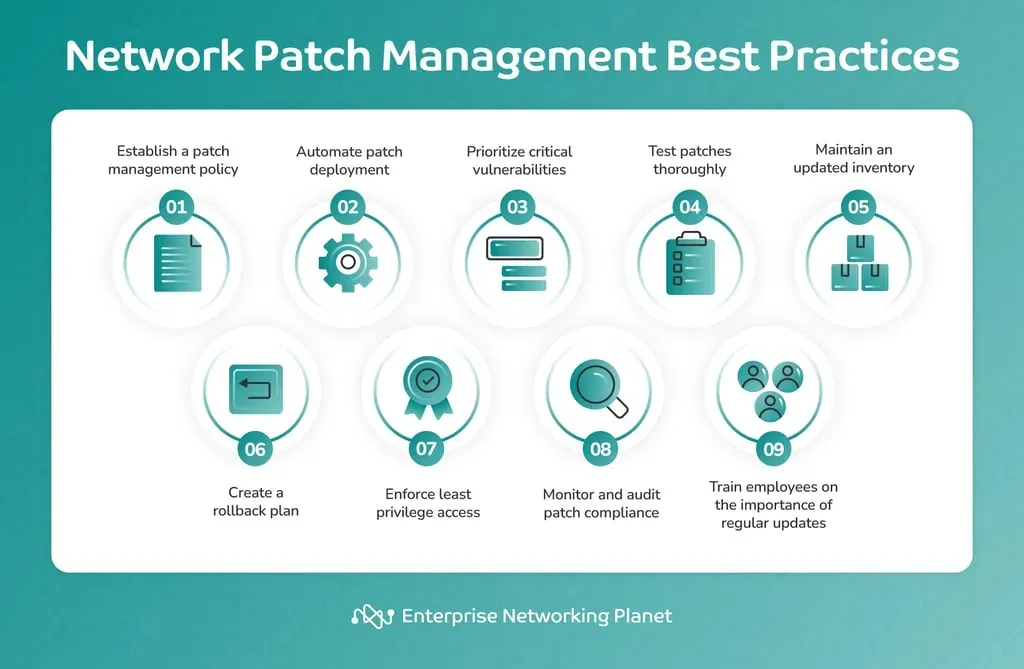
To operationalize Patch Management Best Practices, establish clear governance, policy, and responsible ownership. Tie patching to change management, maintenance windows, and regulatory requirements so deployments are predictable and auditable. The phrase Patch Management Best Practices anchors this guidance, while weaving in concepts from the patch management guide, IT patch management, and patch deployment best practices.
Develop a risk-based prioritization framework that aligns with business priorities, automates routine tasks where possible, and documents exceptions. Emphasize testing, rollback planning, and verification to confirm that patches are installed correctly and do not disrupt mission-critical applications. This approach is consistent with software update management and vulnerability remediation through patching, ensuring durable security gains.
Automation and Tooling: Accelerating IT Patch Management
Automation dramatically improves the efficiency and reliability of patch management. Endpoint management platforms provide centralized patching, OS updates, and software update management across Windows, macOS, and Linux, enabling automated scanning, patch approvals, and scheduled deployments.
Supplement automation with patch catalogs, software deployment services, and server/cloud patching solutions to maintain visibility and control while reducing manual intervention. Integrating with change management ensures deployments are approved and auditable, further strengthening vulnerability remediation through patching as part of a proactive security program.
Risk-Based Prioritization and Patch Deployment Strategies
Not every patch requires immediate action. Prioritize critical and high-severity patches for internet-facing systems, domain controllers, and security gateways, using CVSS scores and asset criticality to guide decisions. Schedule routine updates during maintenance windows and reserve rapid response for zero-day or actively exploited vulnerabilities, following patch deployment best practices.
Include automated validation checks after deployment, such as health checks and application responsiveness, and maintain rollback options in case issues arise. This risk-based approach aligns with IT patch management principles and supports vulnerability remediation through patching without causing unnecessary business disruption.
Compliance, Auditability, and Continuous Improvement in Patch Deployment
Patching programs should produce auditable evidence of patch status, configuration baselines, and remediation timelines to support regulatory compliance and internal policies. Regular dashboards showing patch coverage and time-to-patch reinforce governance and demonstrate progress to auditors.
Finally, adopt a culture of continuous improvement. Collect metrics like patch compliance rate, mean time to patch, and vulnerability remediation through patching outcomes, then refine inventory, testing, and deployment processes accordingly. This ensures that IT patch management remains aligned with operational goals and security posture across endpoints, servers, and cloud resources.
Frequently Asked Questions
What are Patch Management Best Practices and how do they reduce risk for an organization?
Patch Management Best Practices establish a repeatable, governance-driven process to discover assets, assess vulnerabilities, prioritize fixes, test in staging, deploy with automation, and verify success. By aligning patches to risk and applying vulnerability remediation through patching, organizations reduce exposure, minimize downtime, and maintain compliance across endpoints, servers, and cloud resources.
How can I use a patch management guide to start implementing Patch Management Best Practices?
Follow a patch management guide that covers inventory, vulnerability assessment, patch discovery, testing, deployment, and governance. Build an accurate asset registry, map vulnerabilities to CVEs, apply risk scoring, and establish a standard testing and rollout process to support Patch Management Best Practices.
Why is IT patch management critical and how should you prioritize patches by risk?
IT patch management is the ongoing process of identifying, prioritizing, and applying fixes to vulnerabilities. Use asset criticality, CVSS scores, exploit likelihood, and downtime impact to prioritize patches, focusing first on high-risk, internet-facing, or mission-critical systems and driving vulnerability remediation through patching.
What are patch deployment best practices for reliable updates?
Adopt patch deployment best practices that emphasize automation, centralized patching tools, and a controlled staging environment. Validate patches for compatibility, perform health checks post-deployment, implement rollback plans, and ensure changes go through approved change management to minimize user impact.
How does software update management fit into Patch Management Best Practices?
Software update management is a core component of Patch Management Best Practices, ensuring timely OS and application updates across endpoints, servers, and cloud resources. Leverage patch catalogs, automate rollout, and coordinate with maintenance windows to maintain security and availability.
How can you measure success in patch management and vulnerability remediation through patching?
Measure success with metrics such as patch compliance rate, mean time to patch, time to verify patch installation, and the number of remaining unpatched vulnerabilities. Use dashboards and governance reviews to demonstrate progress and the effectiveness of vulnerability remediation through patching.
| Topic | Key Points |
|---|---|
| Definition and Goals |
|
| Inventory and visibility |
|
| Vulnerability assessment and risk scoring |
|
| Patch discovery and prioritization |
|
| Testing and staging |
|
| Deployment and verification |
|
| Post deployment review and governance |
|
| Automation and Tools for Efficient Patch Management |
|
| Risk Based Prioritization and Patch Deployment Best Practices |
|
| Testing and Staging as a Guardrail |
|
| Compliance, Security, and Auditability |
|
| Common Pitfalls and How to Avoid Them |
|
| Measuring Success and Continuous Improvement |
|
Summary
Patch Management Best Practices establish a disciplined, repeatable approach to securing and maintaining software across endpoints, servers, and cloud resources. This descriptive conclusion emphasizes how a mature patch program reduces risk, minimizes downtime, and ensures regulatory compliance through a well-defined lifecycle, automation, governance, and continuous measurement. Organizations leveraging these practices can stay ahead of threats while delivering reliable services.